In most organizations security issues are the responsibility of many teams. Each of them manage only a selected part of the infrastructure. Some administrators handle the network, some only servers. There is no global view of the entire environment. To solve this problem the concept of the Security Operations Center (SOC) arose which involves combining security information from multiple sources in one central place. Based on the SOC model, EMCA SA has created a unique application called Security and Informational Events . The offered solution integrates the Flowmon solution with the Splunk platform.
Integrated technologies
Splunk Enterprise is a platform for collecting and analysing of machine data generated from technology infrastructure, security systems and business application. Using machine data Splunk is able to address big data, IT operations, security and analytics use cases. Solution helps operators to gain operational intelligence from the machine data and makes task of troubleshooting and investigating of security incidents faster and easier.
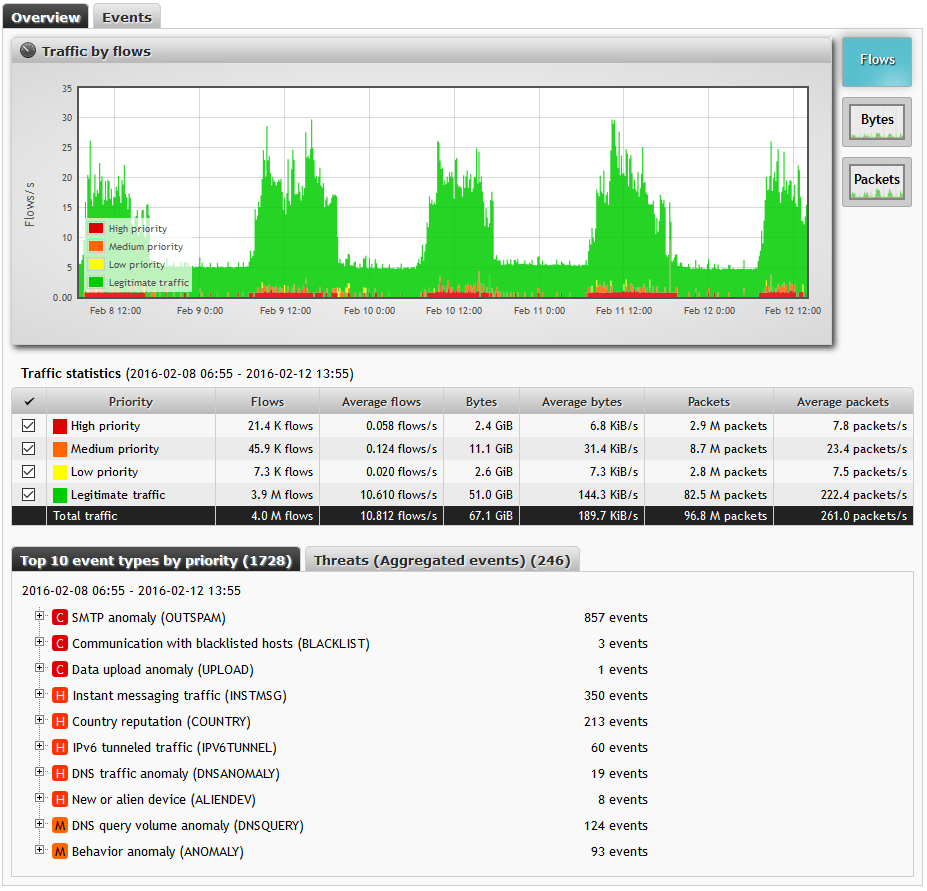
Flowmon >is the market leader in network traffic monitoring and analysis based on NetFlow/IPFIX. Solution efficiently and transparently monitors network traffic inside LAN/WAN, providing insight to network communications and performance. Equipped with Flowmon ADS (Anomaly Detection System), solution is able to automatically detect network anomalies and other security threats and removes from the operator the need for constant security analysis of network traffic.
Security and Informational Events (S&IE) is a Splunk environment application created by the EMCA team that allows a way to obtain a single view for log analysis and traffic in a security context.
Application
Logs from various devices goes directly to the Splunk platform. The created application - S&IE - first does a log correlation stored in Splunk for the automatic detection of incidents in the IT area. A network area view is obtained from Flowmon as a result of integration with this platform. Flowmon collects and analyse NetFlow, IPFIX or sFlow statistics about network traffic using the data from flow-enabled devices such as routers, switches and firewall or Probes deployed on SPAN ports or TAPs. The Flowmon ADS module performs the continuous analysis of network behavior. It uses built-in analytical methods and algorithms which can detect configuration errors, violations of security policies or changes in network behavior. The used mechanisms can detect zero-day attacks, advanced persistent threats, or other security incidents. Implemented rules dynamically react to detected events and provide alerts at the appropriate level of severity to help assess the risks.
Figure 1: Flowmon ADS dashboard
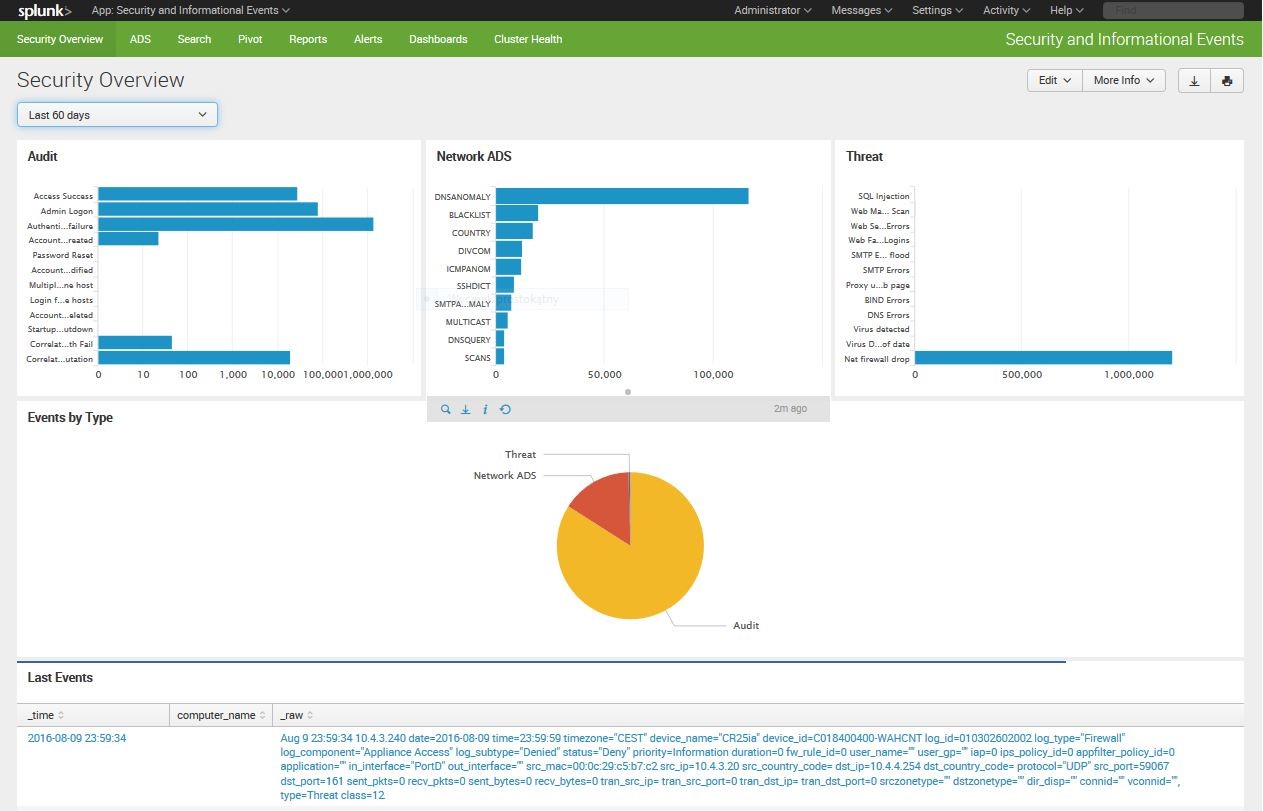
Information about threats detected by Flowmon ADS are sent to Splunk to previously prepared S&IE indexes (event data repository). S&IE user can observe all incidents in real time. Incidents are divided into three categories:
- Audit – log analysis from operating systems
- Network ADS – network incidents
- Threat – vulnerabilities from AV/IPS/IDS systems
Various graphs display the type of events that have occurred in a considered time period. The pie chart shows the portions of each category from all the events.
Figure 2: Security and Informational Events - security console
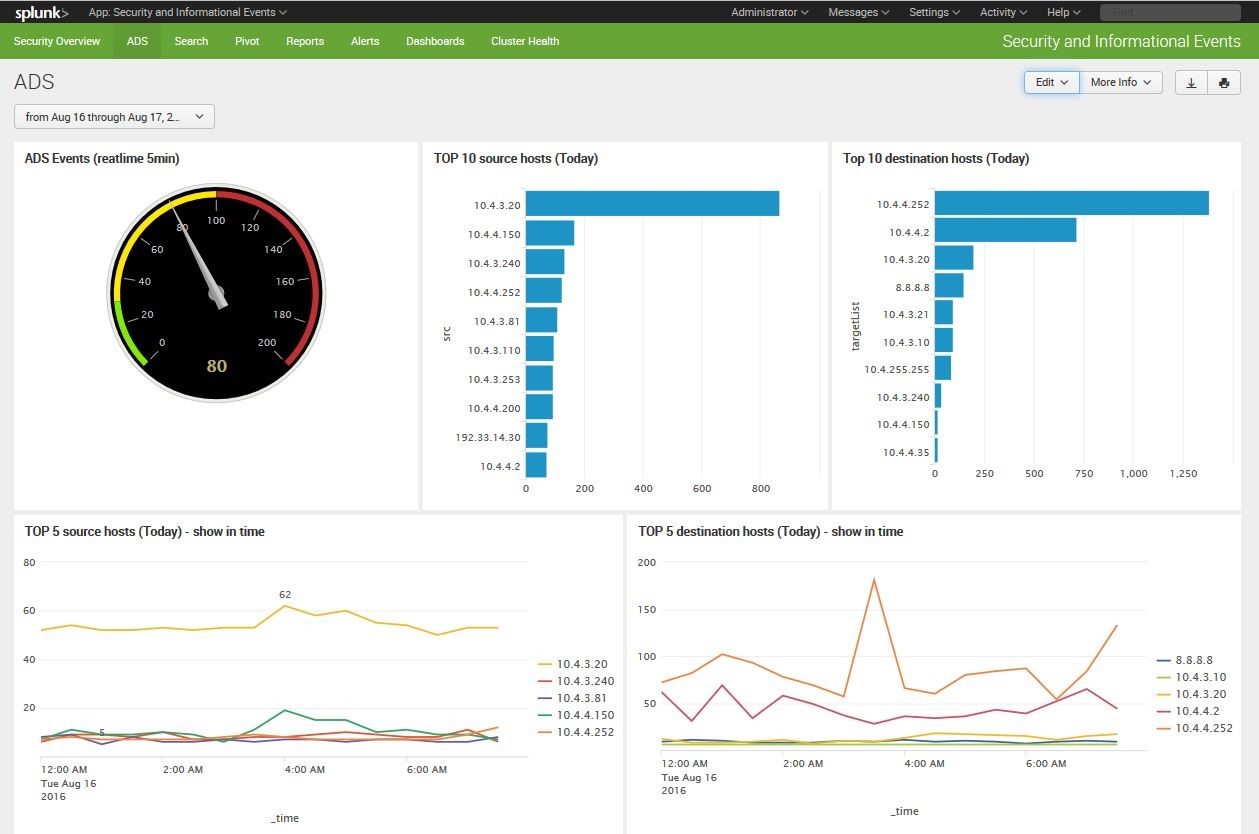
The application created by EMCA - Security and Informational Events (S&IE), allows operators to gain more details about each event sent by the Flowmon system. Incidents reported by Flowmon ADS are grouped according to the source and destination hosts and subjected to additional statistical analysis. This is presented by the application GUI in a separate window called ADS.
Figure 3: Security and Informational Events - dedicated console for ADS
The presented integration allows to build an analytical environment that delivers appropriate information for different groups of interested users.
About Partner
EMCA SA is full-service IT company specializing in a IT infrastructure monitoring, network monitoring and big data analytics, machine data and enterprise security. EMCA SA provides software licensing, deployment and professional services, and post-sale support.
Flowmon Networks Gold Partner
Splunk Premier Partner