Every organization has its network perimeter and end-points secured. But in the world of advanced threats, breaches still happen and time to detect such security incidents is too long. Combining features of Palo Alto Networks NGFW (Next-Generation Firewall) and Flowmon ADS, you can achieve additional layer of security . Today we will take a look on how to configure Palo Alto NGFW to export NetFlow data which are analysed in Flowmon ADS to detect threats that can bypass traditional security solutions.
Palo Alto NGFW flow export configuration
Palo Alto NGFW NetFlow export is configured in three basic steps.
- Define new NetFlow server profile.
- Assing created profile to firewall interface.
- Change the exporting interface (optional).
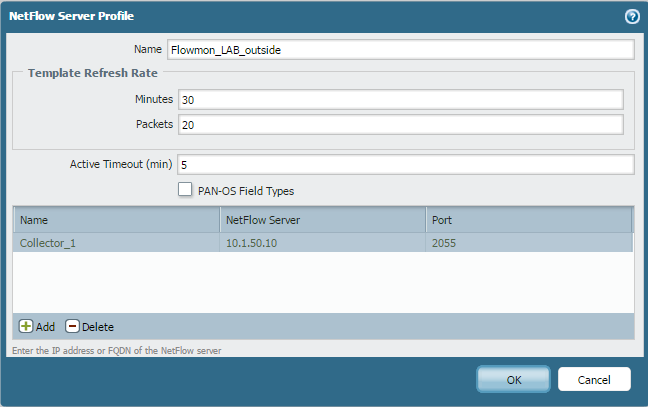
First step is to define new NetFlow server profile. In the GUI, navigate to Device tab → Server Profiles → NetFlow. Configuration is pretty straight forward:
Enter a Name for the NetFlow Server Profile.
Set Template Refresh Rates (number of minutes or packet after which the NetFlow template is sent to collector), we recommend 4096 packets and 5 minutes.
Set Active Timeout (how long does it take to export flow data for each session) to 5 minutes.
Add NetFlow Server specifying the Name of the server, NetFlow Server IP address and Port number of the collector’s listening port.
Figure 1: New NetFlow server profile definition.
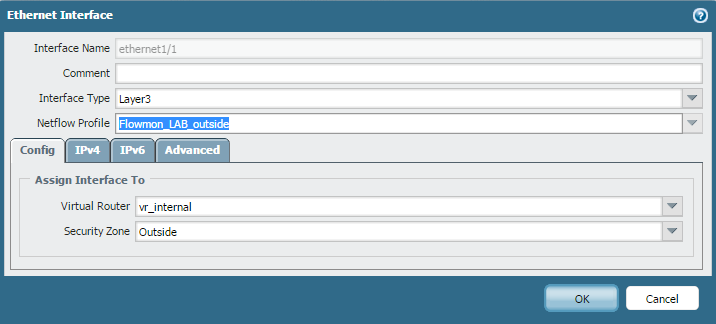
Second step is to assign the configuration of the profile to the firewall interface from which Netflow data will be generated. Navigate to Network → Interfaces → Ethernet. Here, select any interface and assign the NetFlow Profile created in the first step.
Figure 2: Assigning profile to firewall interface.
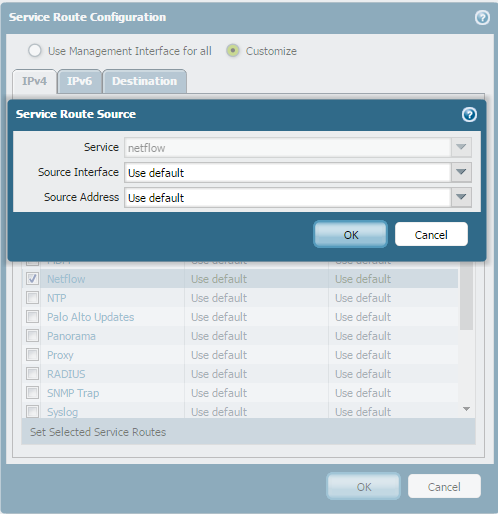
Last step is optional. By default, the firewall uses management interface to export flow data to the NetFlow server. However, it is possible to change the interface to another Layer3 type interface. This can be configured in the Device tab → Setup → Services → Service Route Configuration.
Figure 3: Changing exporting interface.
Check the reception in Flowmon
Now we have NetFlow export from Palo Alto NGFW up and running. To check NetFlow data stream from Palo Alto NGFW, go to Flowmon Monitoring Center → Sources . Flowmon Collector is automatically detecting devices exporting flow data to it’s listening ports, so if you had configured listening ports before you configured NetFlow export, you should see graph with the data. Otherwise, go to Configuration Center → FMC Config → Listening ports and configure the listening port to match it with NetFlow Server Profile of Palo Alto NGFW.
If you are receiving the data, go to the Flowmon ADS module in the tab Processing → Flow Sources and check if you are analysing the right profile and channel (NetFlow data from Palo Alto NGFW).
Benefits
Integration of Palo Alto Networks NGFW with the solution of Flowmon Networks based on flow technology, provides an additional layer of infrastructure protection and correlation of events by making full use of the knowledge possessed by the firewall on the transmitted traffic. Joining both solutions, you are provided with benefits like:
- Visibility into network traffic before / after firewall.
- Detection of external and internal threats.
- Visibility of network traffic inside the network.
- Protection against advanced threats that can bypass traditional security protection tools.
Interested in more details?
If you already have Palo Alto NGFW deployed on your network perimeter and want additional layer of security, try our free trial version of Flowmon Collector with Flowmon ADS. Download package contains quick start guides to set up additional layer of security in no time.
After you are successfully started analysing NetFlow data from Palo Alto NGFW, be sure to tune up the Flowmon ADS to get the best accuracy of detection. To help you to tune Flowmon ADS in an hour, we have created tips and tricks for you.
Want to know more details about the configuration of Palo Alto NGFW flow export? Contact us and we will send you detailed guide made by our partner Clico in Poland.
