Flowmon Probe NetFlow and IPFIX Exporter
The Flowmon Probe is the most powerful flow data exporter on the market that generates data down to the application level and measures performance.
Use it anywhere
Hardware, virtual or cloud, from 10 Mb/s to 100 Gb/s.
Stay non-intrusive
The Probe connects passively through a SPAN port or network TAP.
Reduce noise
Network data is pre-filtered to enable clearer analysis and visualization.
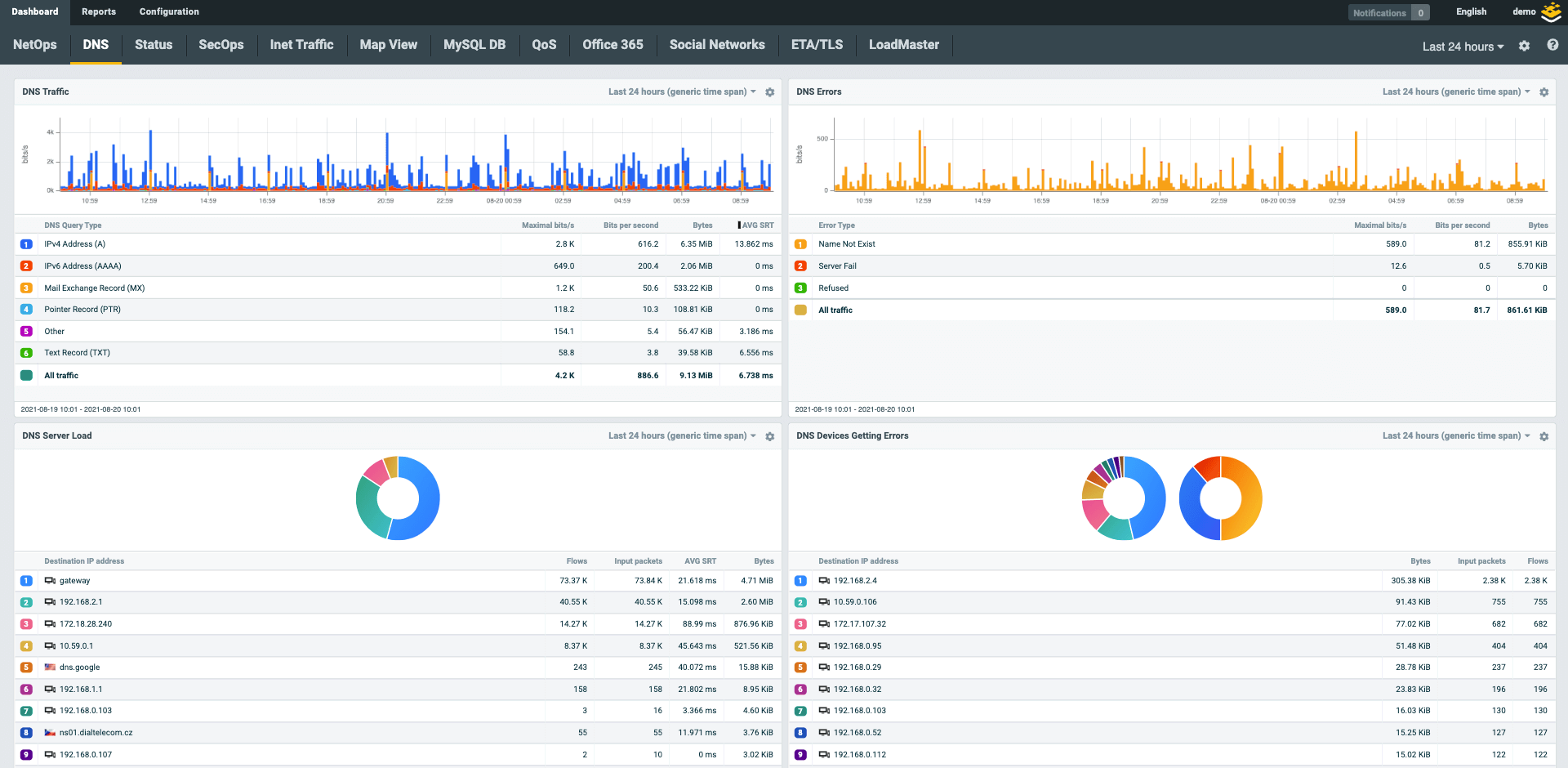
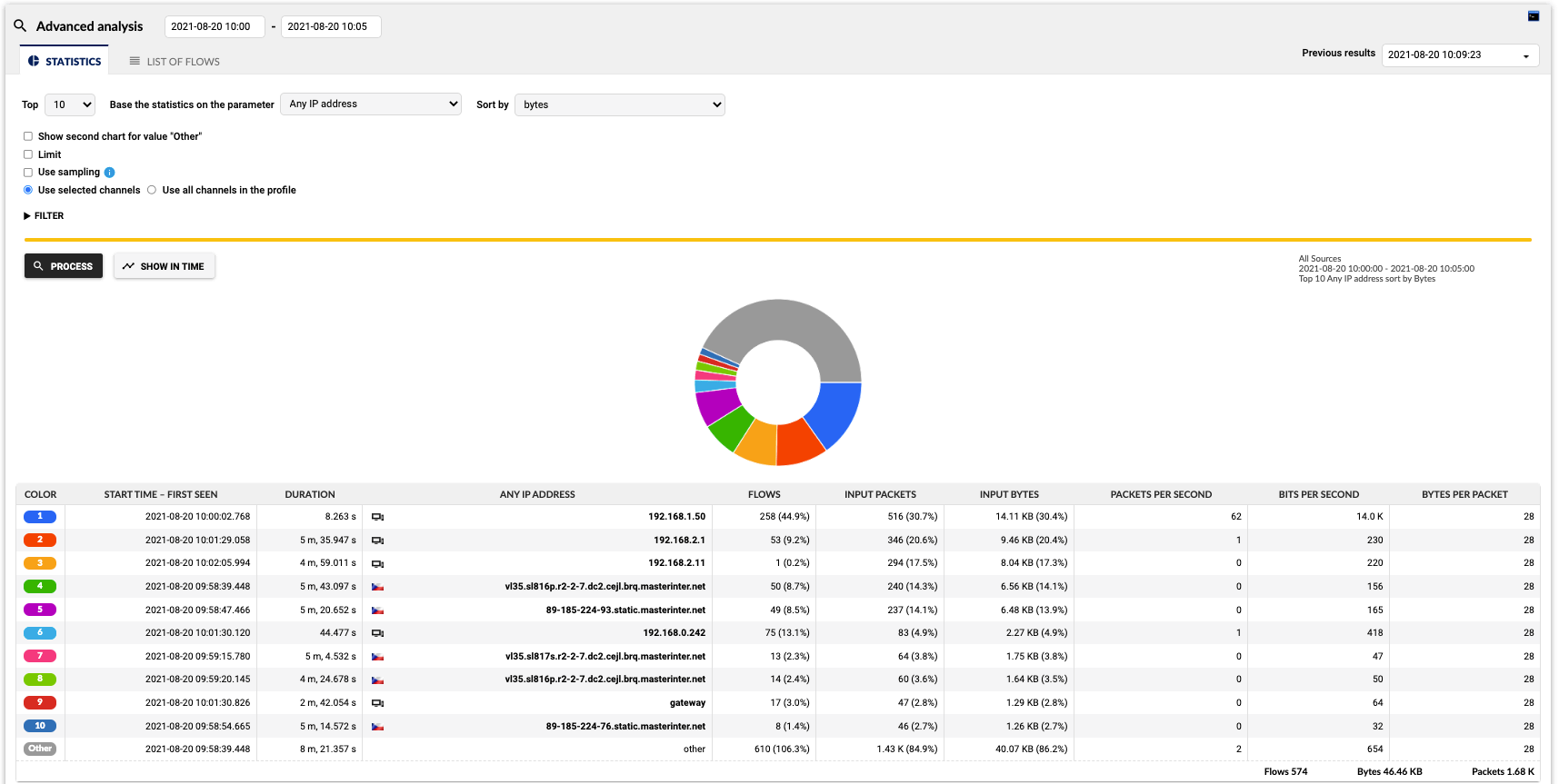
Visibility into L2, L3/4, L7
Probes natively collect L2–L4 information on IP addresses, protocols, server response time, round trip time, jitter, and more, while leveraging traffic decapsulation to monitor the real user-application conversation instead of the tunnel itself. In addition, Flowmon's IPFIX extension provides additional L7 data, such as hostnames, URLs, browser information for HTTP/S protocols, and other fields for protocols like DNS, DHCP, SQL, SMTP, or Samba/CIFS, and more.
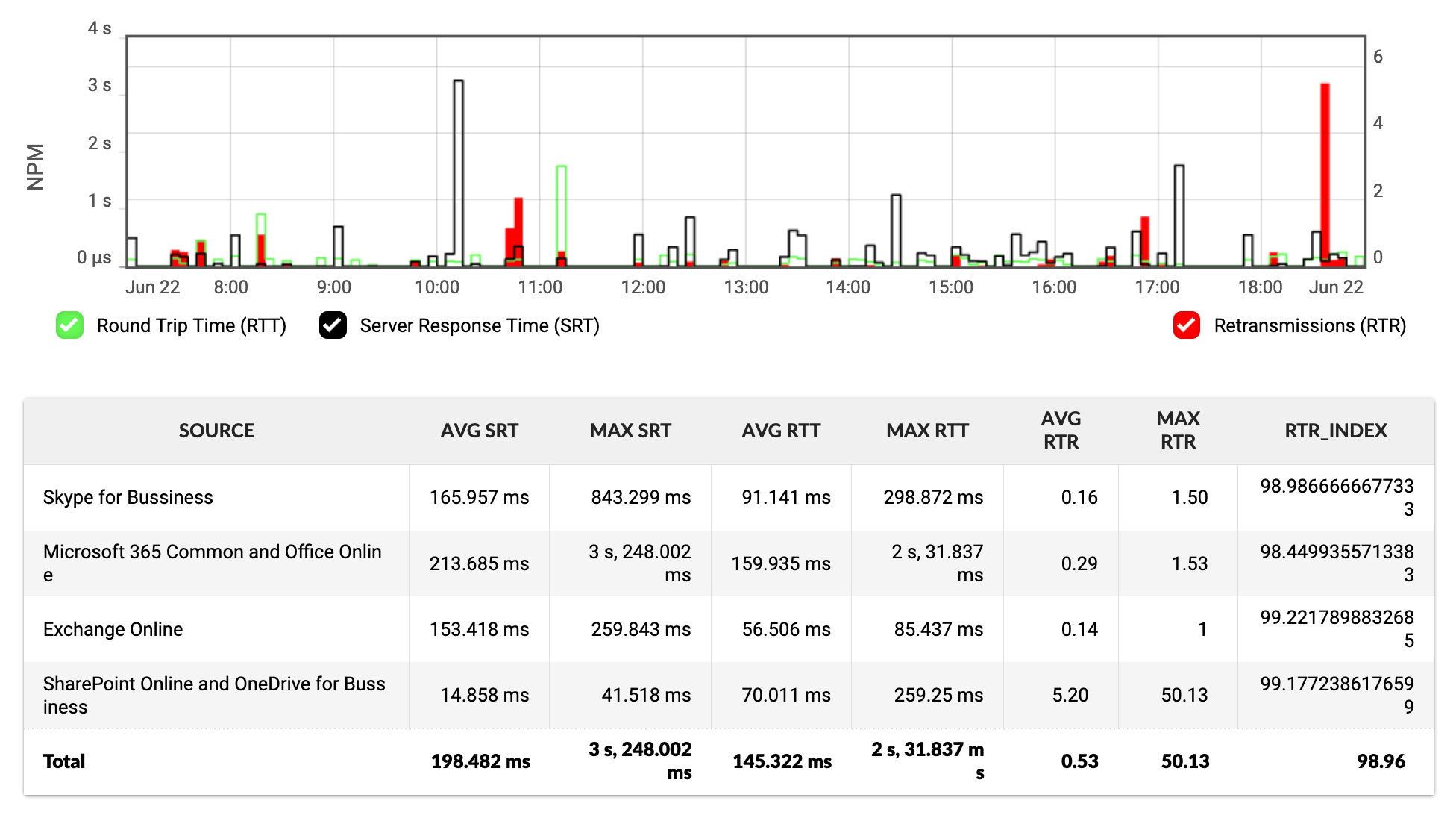
Network Performance Monitoring
Leveraging a wide array of metrics, it enables insight into the performance of the network. The Probe measures server delay (Server Response Time) and network delay (Round Trip Time), as well as Jitter, TCP Retransmissions or out-of-order packets.
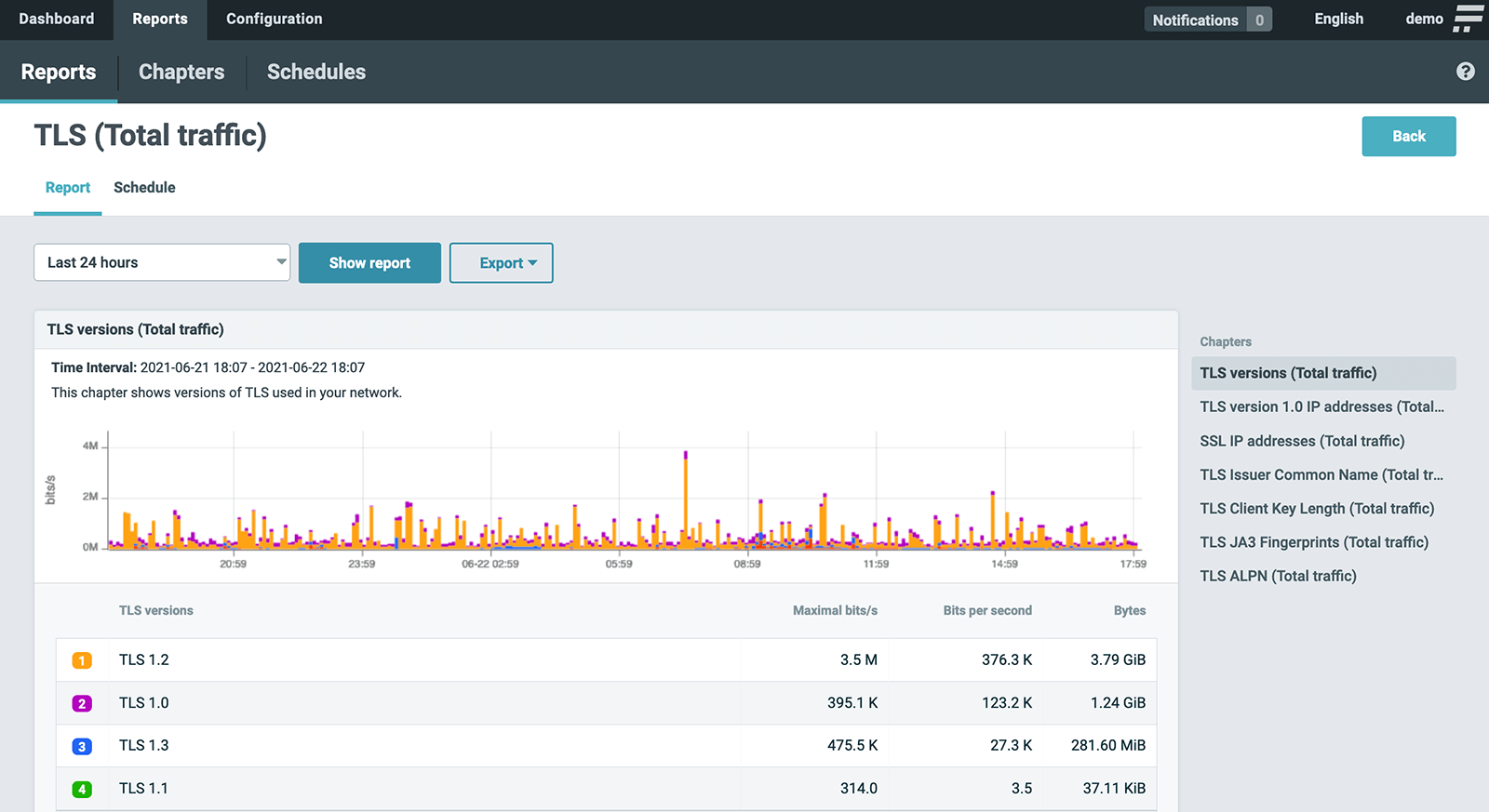
Encrypted traffic analysis
Flowmon’s encrypted traffic analysis collects network traffic metadata in the IPFIX format using Probes and enriches it with TLS protocol information. This provides a wealth of information about the traffic and allows for the identification of out-of-date SSL certificates, policy non-compliant certificates, encryption strength and old TLS versions that may contain faults or vulnerabilities.
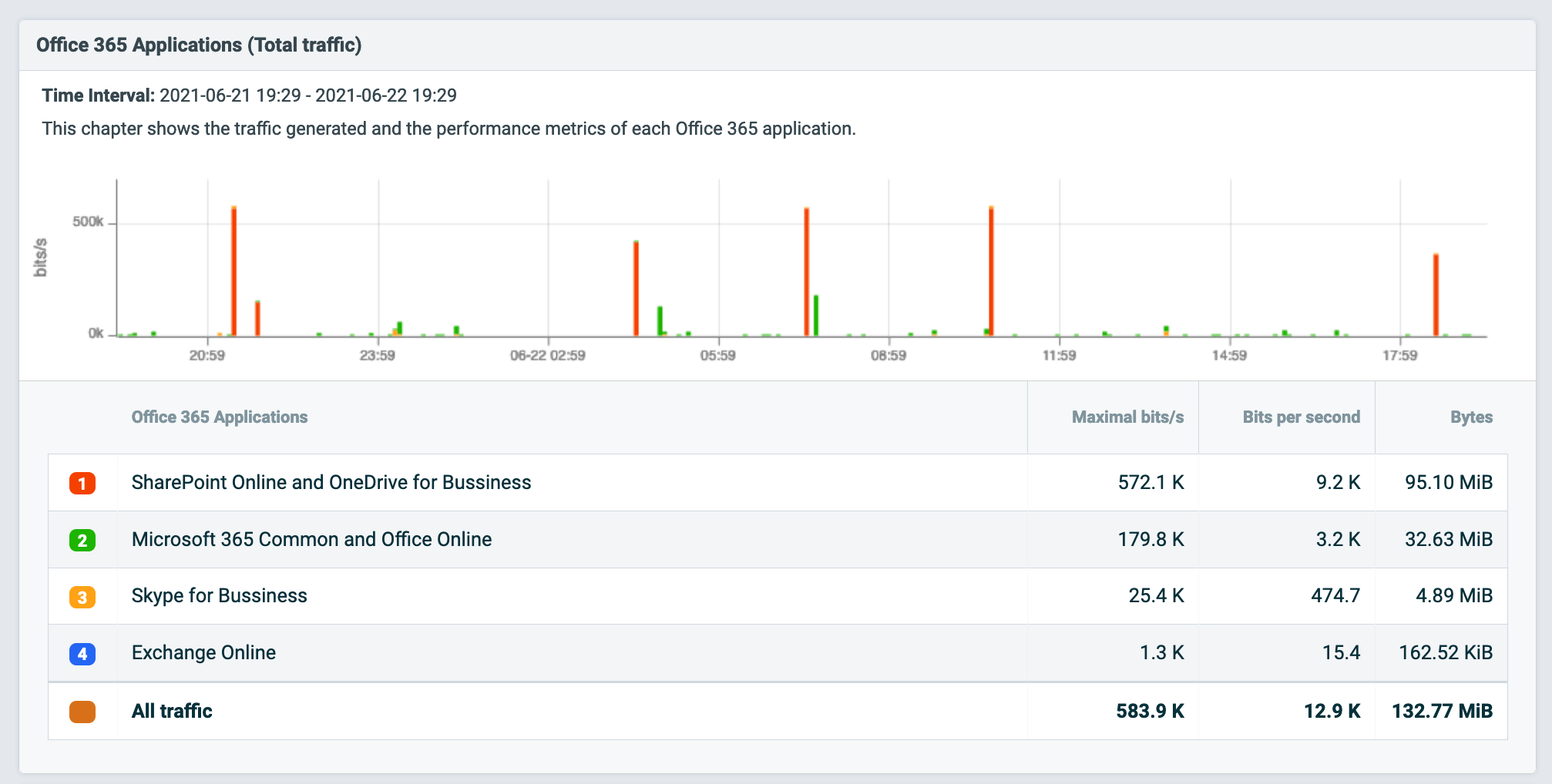
Application recognition and usage data
Flowmon reports on the use of applications by analyzing L7 packets and exporting Network-Based Application Recognition (NBAR2) name or provides information on the source or destination of network traffic with the Autonomous System (AS) number.
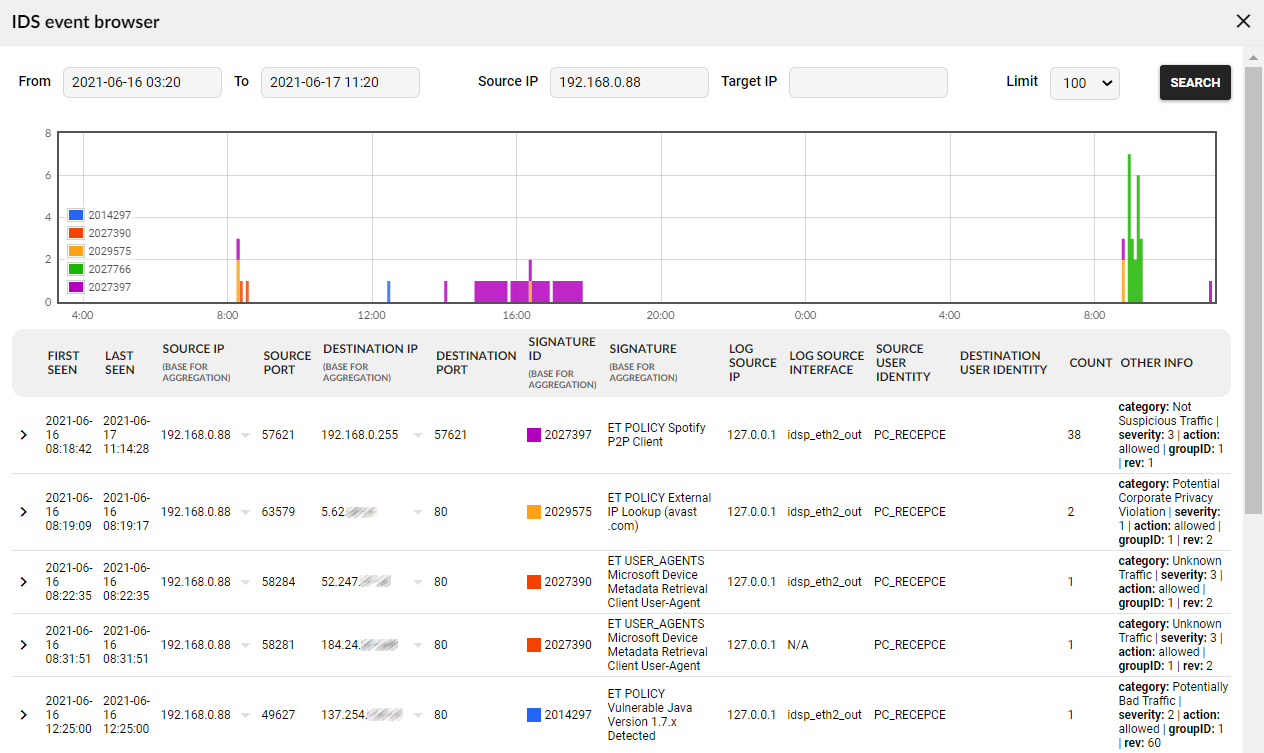
Flowmon IDS Probe powered by Suricata
Using Flowmon IDS Probe powered by Suricata enables packet inspection to seek potential intrusion, complementing the signature-less approach of Flowmon ADS and providing an additional level of security. The extension works in environments of any link speed from 1 Gb/s to 100 Gb/s, and the detected events may be exported to any target.
Deploy anywhere in minutes
The Flowmon Probe can be deployed in any kind of network without an impact on network traffic at speeds of 10 Mb/s to 100 Gb/s. Virtual Probes can be deployed in virtual environments such as VMware, Hyper-V, KVM, or as a cloud application in AWS, Azure and Google Cloud.
Request free trial
Get no-obligation 30-day trial of Flowmon in your network.
Get your trial todayRead more about the Probe
Flowmon Probe Models Specification