Flowmon – A flexible Darktrace alternative that scales
Packet analysis utilized by Darktrace scales poorly and has enormous storage requirements. But Flowmon relies on flow-based NDR supplemented by on-demand or on-event packet capture, providing more performance per appliance and weeks of storage history.
Enterprises you trust use Flowmon





Detect ransomware, expose insider threats, respond immediately
- No blackbox – understand security events and their consequences.
- Scale up easily with future-proof technology for hybrid and multi-GB enterprise environments.
- Easily integrate to reinforce your security matrix (log management, SIEM, SDN, IR, etc.).
- Leverage advanced detection and response capabilities at a fraction of the price.
- Break down the silos between NetOps and SecOps and ensure security and resilience of your network with one tool.
See live product demo
Explore a fully interactive product of Flowmon and see what issues it can tackle.
Flowmon vs Darktrace
| Flowmon | Darktrace | |
|---|---|---|
Scalable technology Network telemetry supported by on-demand packet analysis. | ||
Leveraging existing infrastructure Using existing infrastructure as a data source maximizes investment. | ||
Out-of-the box functionality Deploy in hours with minimal vendor assistance. | ||
Broad customization options Adjust the solution to fit into your security ecosystem. | ||
Extensive reporting Get detailed human- and machine-readable reports. | ||
Top performance per a single appliance High throughput means broader coverage by one appliance and less budget strain when your network grows. | 2x100Gbps / 2x100Gbps throughput | 2x10G / 5 Gbps throughput |
NetOps functionality Insights for network troubleshooting and bandwidth monitoring. | ||
Flexible pricing A cost-effective plan that scales with your business. |
Try the features in demo or continue to learn more
Instant threat detection
Kemp Flowmon features over 40 detection methods and more than 200 algorithms to pick up subtle changes in network traffic and expose the malicious activity of unknown and insider threats operating in the network including encrypted traffic. In addition to signatureless detection, it leverages the signature-based Suricata IDS and MISP threat intelligence feeds.
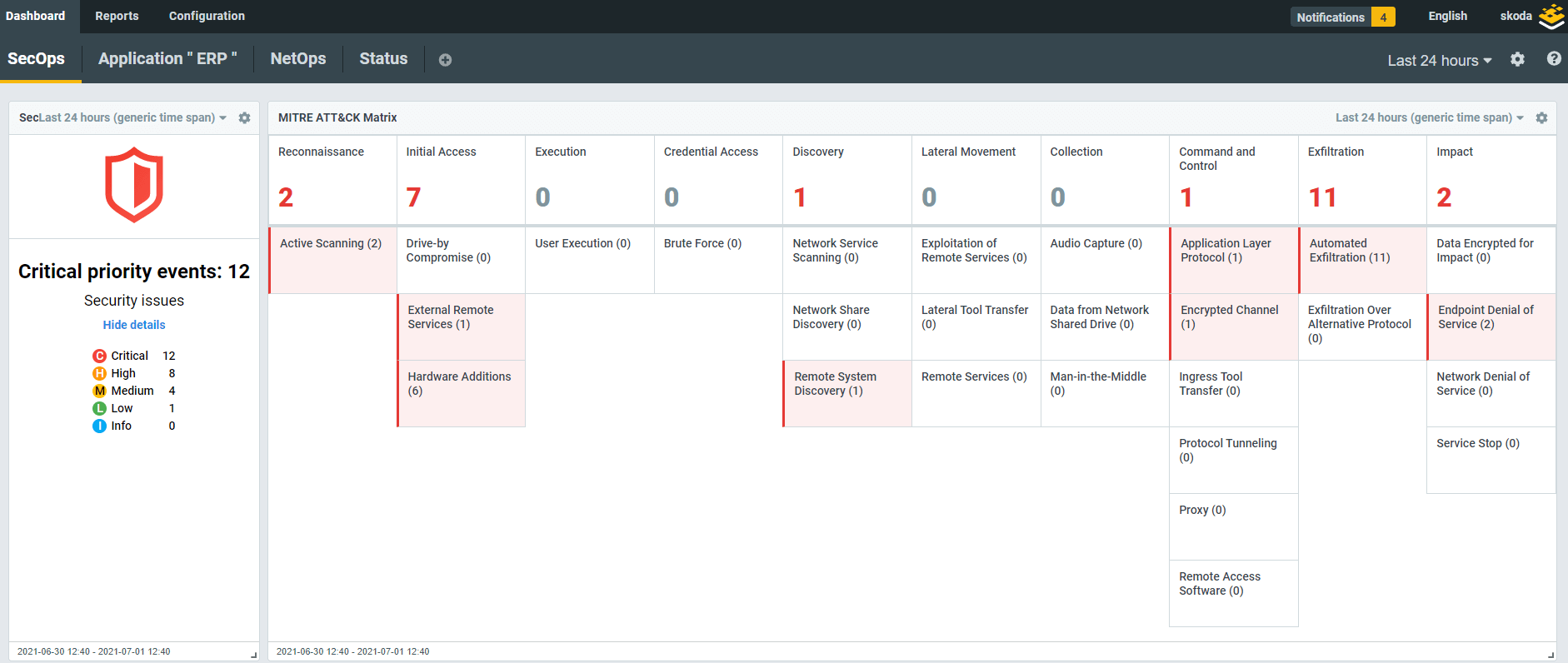
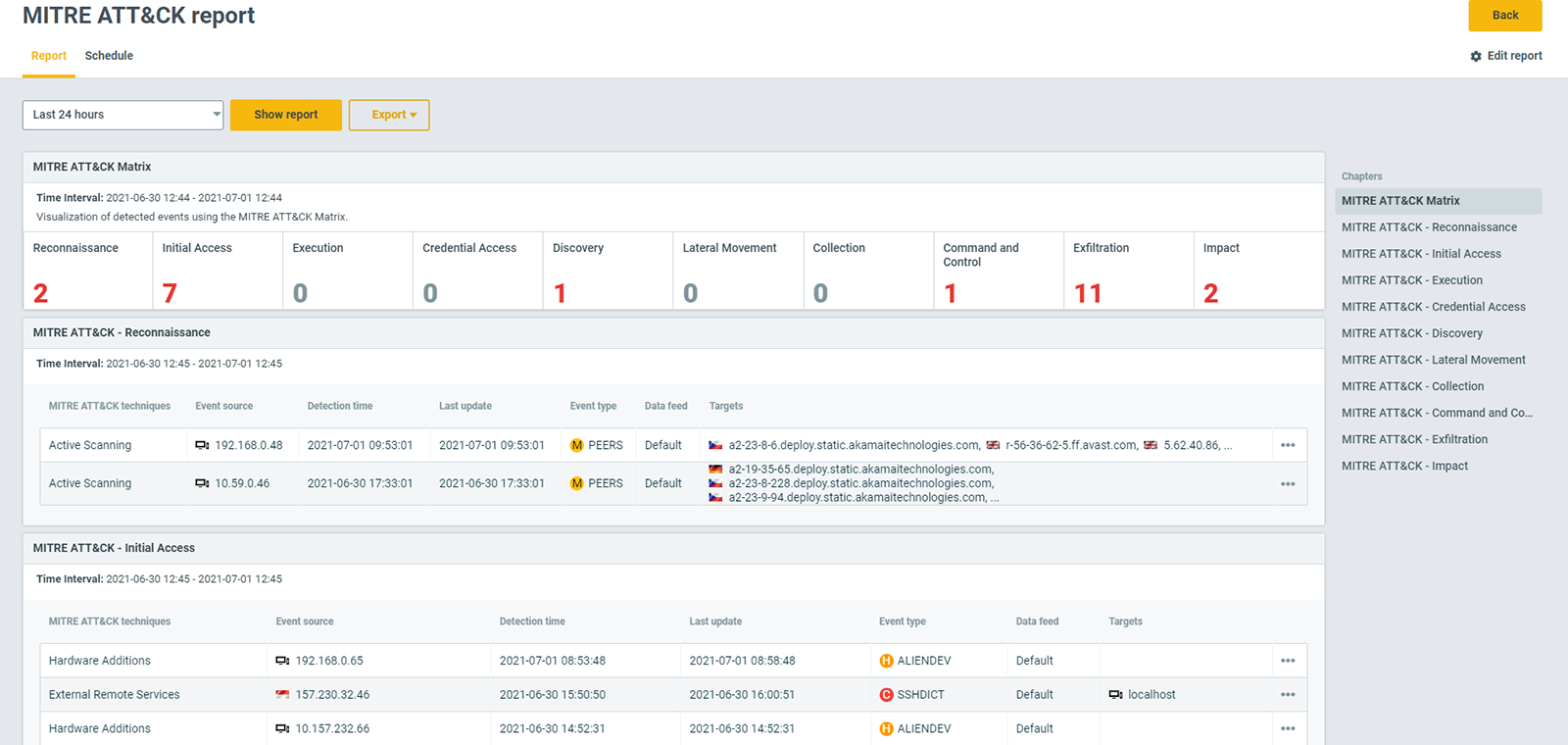
Context awareness
Security events are visualized on zero-clutter dashboards and ranked by severity. Kemp Flowmon also categorizes them according to MITRE ATT&CK tactics and techniques to give you an at-a-glance understanding of the compromise stage, scope and future development.
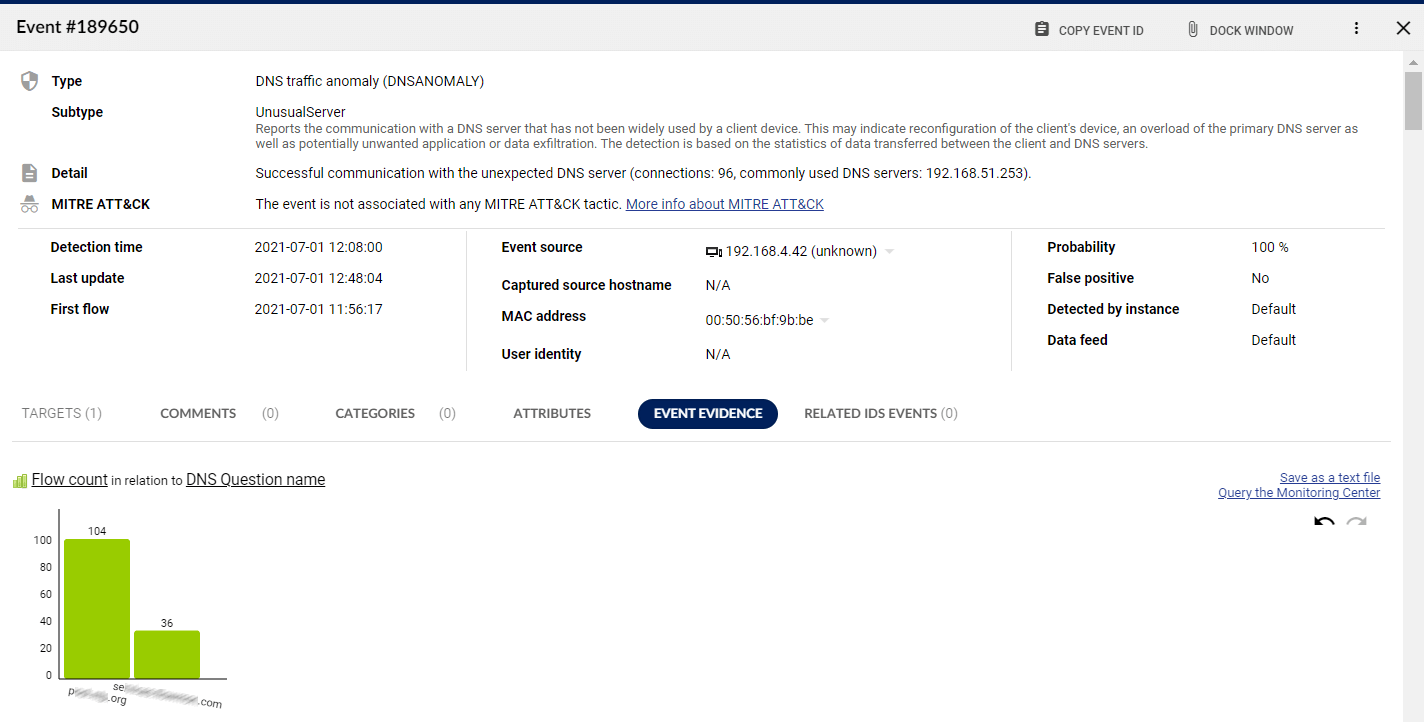
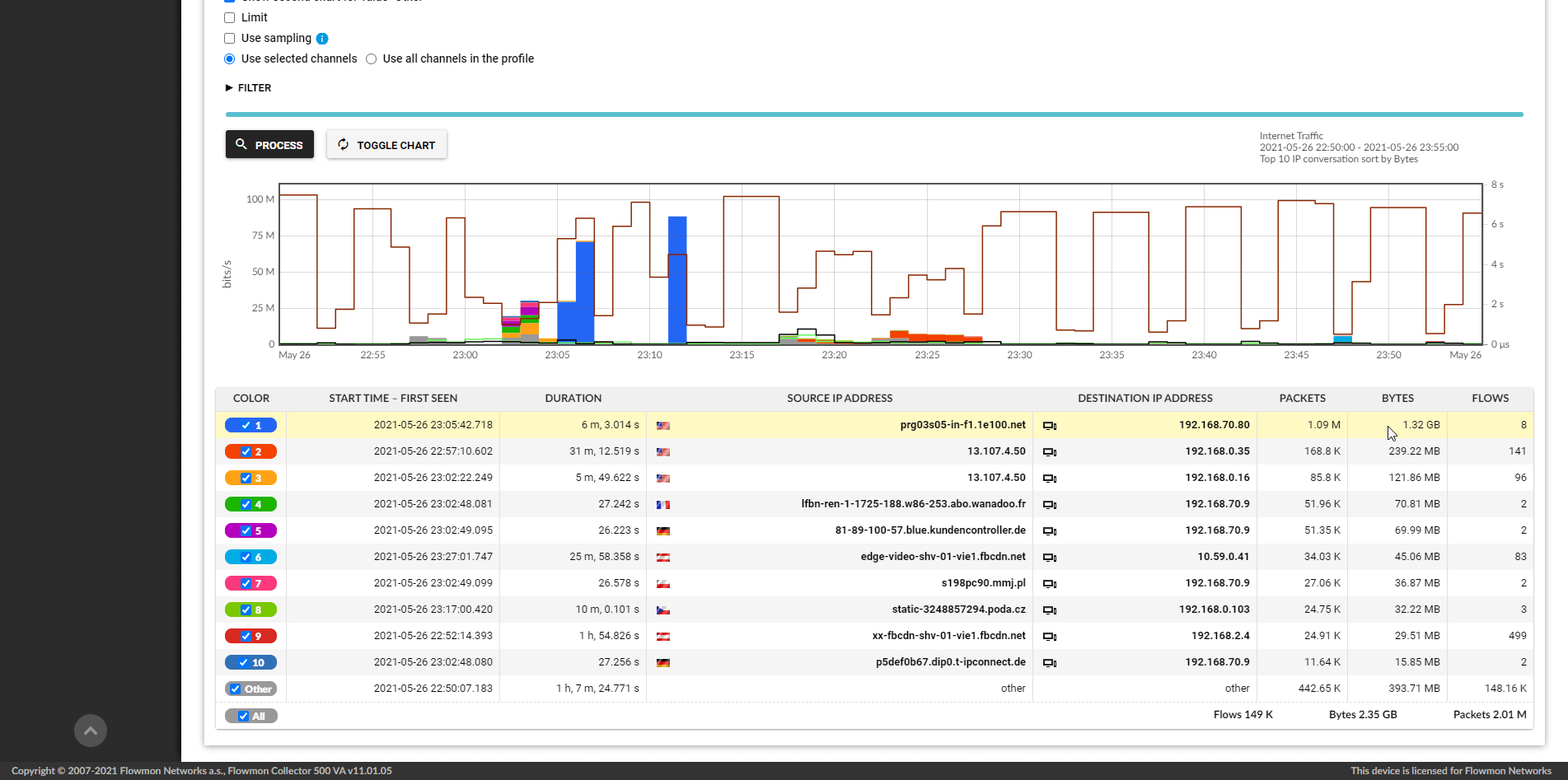
Analytical workflow
You can access detailed information about every event from anywhere on the dashboard and extract insights such as the timeframe of the event, attack target or origin, related events of the incident, or interpretive descriptions of the anomaly.
Future-proof technology
Besides low scalability, proprietary packet-based technology faces additional challenges with traffic encryption and hybrid deployments. Kemp Flowmon is flow-based (NetFlow/IPFIX) and thus perfectly suited to overcome these issues with zero impediment and deliver future-proof, cross-environment security that scales easily while remaining cost-efficient.
Expose unknown threats quickly and efficiently
Get features packed solution with great support.
Maximize investment
Flowmon is up to 500 times more scalable than packet analysis.
Data compatibility
Compatible with all environments for seamless integration.
Top-rated support
Word-class 24/7 support with 5/5 ranking on Gartner Peer Insights.

"After three months of intensive testing we were able to prove that Flowmon was the right product due to its performance, anomaly detection capabilities, scalability in GÉANT and its simplicity when managing and configuring."
Head of Information & Infrastructure Security
Ready to get started?
Try out an interactive demo and experience the capabilities of the most scalable NDR solution on the market.
Start demo now